Google Groups
Spinnaker supports G Suite accounts (formerly Google Apps for Work) and Google Groups to manage authorization.
Fiat (Fix it Again Travis) is the authorization (authz) microservice of Spinnaker. It can grant access to users to execute pipelines, view infrastructure, etc. It is disabled by default. Much like authentication, Spinnaker allows for a variety of pluggable authorization mechanisms.
With Fiat, you can…
Permissions can be attached to applications and (provider) accounts. A permission associates a role with one of these
options: READ, WRITE, or EXECUTE (for apps only).
Keep these in mind as you consider your authorization strategy:
Fiat’s authorization model is an approve list that is open by default. In other words, when a resource does not define who is allowed to access it, it is considered unrestricted. This means:
Every permission in Spinnaker is granted to a role. Individual users cannot be granted permissions. You also grant Super admin access to a role. You may see discussions of users in Fiat’s implementation but it’s just an optimization in the storage to not recompute user → roles → permissions.
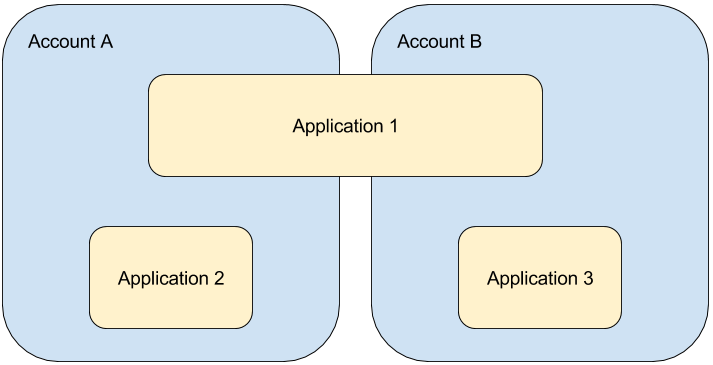
Account and application access control can be confusing unless you understand the core
relationship: accounts can contain multiple applications, and applications can span multiple
accounts. Giving access to an account does not grant access to the application and vice versa. Sometimes you need
both permissions to perform certain actions.
Authentication successfully setup in Gate.
An external role provider from one of the following:
SAML roles are fixed at login time, and cannot be changed until the user needs to reauthenticate.
Enable fiat in the spinnaker.yml file. This enables services to query fiat for auth information.
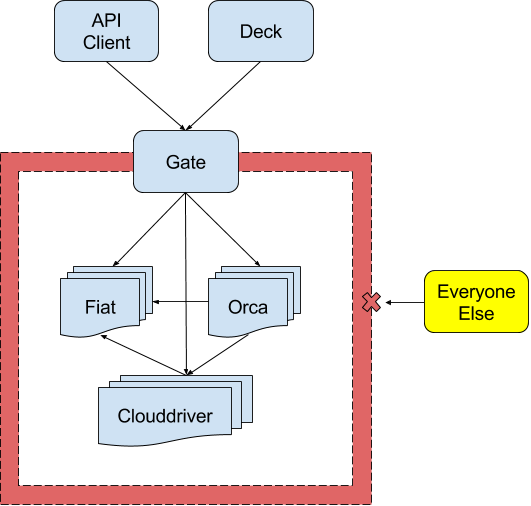
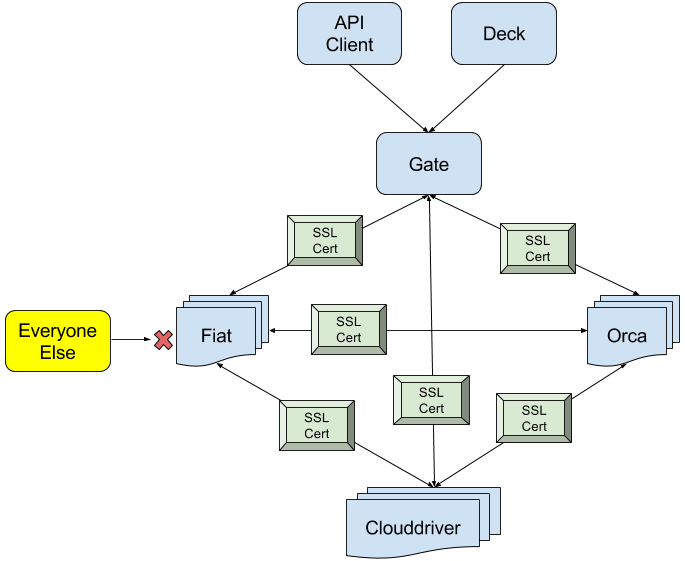
(Highly Suggested) All Spinnaker component microservices are either:
Firewalled off as a collective group, or:
Use mutual TLS authentication:
Because Clouddriver is the source of truth for cloud accounts, Fiat reaches out to Clouddriver
to gather the list of available accounts. There are two types of access restrictions to an account: READ and
WRITE. Users must have at least one READ permission of an account to view the account’s cloud resources, and at
least one WRITE permission to make changes to the resources.
Every cloud provider, and many OTHER account types like those in igor for CI systems can set permissions. You’ll
set these permissions by modifying the account with a permissions set of entries that contain the roles/groups
that you want to grant READ/WRITE permissions.
google:
accounts:
- name: my-google-account
permissions:
READ:
- role1
- role2
WRITE:
- role1
- role2
NOTE That READ permissions ARE NOT implicitly granted by giving WRITE permissions. AS SUCH it’s HIGHLY recommended to ALWAYS add READ to any WRITE access.
Applications have three levels of permissions: EXECUTE, READ and WRITE permissions.
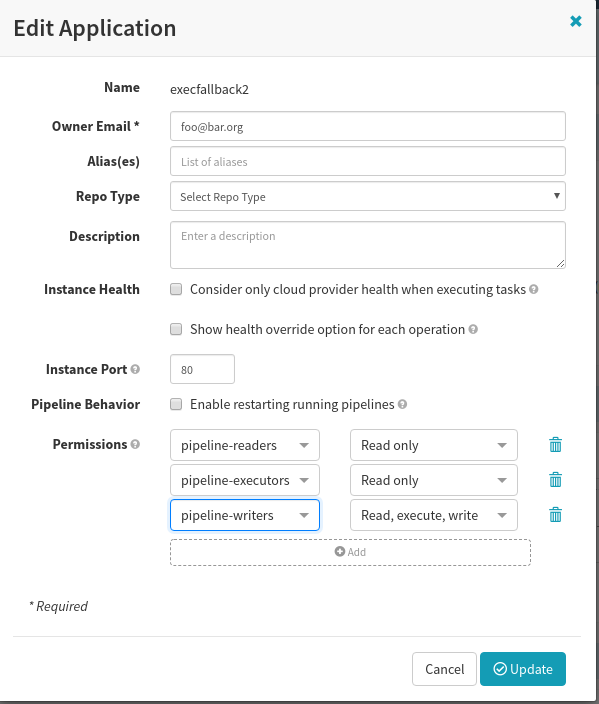
By DEFAULT, READ permissions ALSO grant EXECUTE permissions. To adjust this,
EXECUTE set as needed for your applicationsWRITE users implicit EXECUTE access by
setting the following property in fiat-local.yml:fiat:
executeFallback: 'WRITE'
WRITE permission on the account.WRITE permission on that app.EXECUTE permission.EXECUTE on the app X and
WRITE on the account Y.In Spinnaker there are a few ways you can associate a role with a user:
EXTERNAL. They can be used in addition to authorization roles.In all these methods, users are referenced by a userId which is determined by the authentication method of your choice.
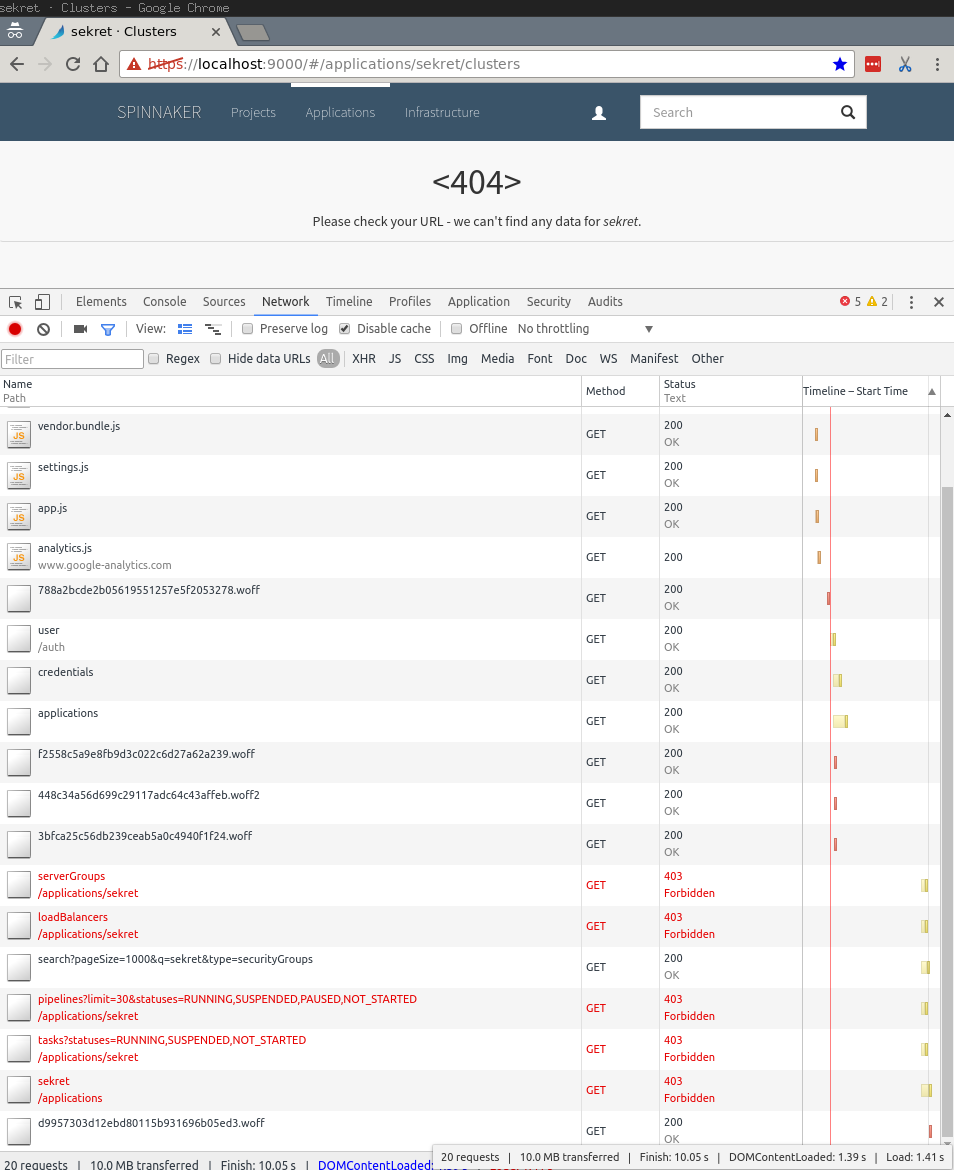
Because of the new access restrictions, https://localhost:9000/#/applications should no longer
list applications that have been restricted. Even navigating to the previously accessible page
should be denied:
A popular feature in Spinnaker is the ability to run pipelines automatically based on a
triggering event, such as a git push or a Jenkins build completing. When pipelines run against
accounts and applications that are protected, it is necessary to configure
them with enough permissions to access those protected resources. This can
be done in two ways:
Deeper details on Authorization in Spinnaker
Spinnaker supports G Suite accounts (formerly Google Apps for Work) and Google Groups to manage authorization.
Spinnaker supports using LDAP for authorization.
Pipeline permissions enable automatically triggered pipelines to modify resources in protected accounts and applications.
Spinnaker supports using SAML for authorization with certain conditions.
Service Accounts enable the ability for automatically triggered pipelines to modify resources in protected accounts or applications.
Spinnaker supports using GitHub teams for authorization. Roles from GitHub are mapped to the Teams under a specific GitHub organization.